What's the difference between a regular firewall appliance and a managed firewall? Do I need a cloud or managed firewall for my business?

What is a managed firewall?
Qualified managed security service providers (MSSPs) typically provide a "managed firewall service "as a solution for firewall operation, administration, monitoring, and maintenance of firewall infrastructure. The MSSP will help establish, maintain, and modify firewall rules, monitor your network, and provide feedback, reports, and analysis.
Depending on the extent of the service agreement, the MSSP may perform firewall installation, application control and web content filtering, as they assist in determining which applications and web content (URLS) to block. They will also help manage patching and updates.
Do you need a managed firewall?
Firewalls are fundamental to protecting network traffic including the flow of sensitive data. They are required for compliance to mandates like PCI DSS, HIPAA, and GDPR. Companies that don't have the personnel resources available to manage their firewall or other security devices can close data security gaps and better prevent data breaches by using a managed firewall service. Most of the companies our auditors work with employ internal IT personnel to manage their firewalls, but many also choose to utilize a reputable managed firewall service so that they can better focus on their core business objectives.
Comprehensive firewall management requires a high degree of expertise and constant vigilance. Firewalls are not a point-and-click or set-it-and-forget-it technology. Purchasing and initially configuring a firewall that is adequate for any given environment is only the beginning.
Whether for compliance or data security alone, a managed firewall service can add significant security to a network.
Common firewall management failures
Our security analysts often encounter serious security risks in the field related to proper firewall configuration and management. Here are a few of the issues they've seen:
Multiple firewalls
A single firewall alone requires regular maintenance and daily monitoring: you need to review rule sets, patch firmware, and update configuration--this work is multiplied with each unique firewall placed in an environment. When there are multiple firewalls and staffing is either insufficient or lacking critical skills required to maintain them, serious security issues can be overlooked, resulting in the loss or compromise of critical data.
No firewall auditing
Firewall auditing, where a company checks and audits their firewall rules regularly, is often left undone. One benefit of contracting with an MSSP is that most providers will perform regular firewall audits as a primary element of their core services.
For example, an auditor reported that at a prominent health organization, no IT personnel had logged in to review the firewall configuration for two years. The auditor discovered a VPN connection linking the firewall to the previous IT employee's home network. This organization was not successfully managing their firewall and as a result, the sensitive data in their network was at significant risk.
Misunderstanding how firewalls work
There are concepts in firewall management that not all IT personnel are familiar with. The area between the externally facing network and internally facing network (known as the "demilitarized zone" or DMZ) must be secure. One audit revealed that certain firewall ports/services were left open on either side of the DMZ, leaving the network exposed and vulnerable to external malicious activity, and the company did not initially see this as a problem.
Inexperience and lack of oversight
IT personnel are often expected to just "make things work." There is tremendous pressure to keep systems up and running for day-to-day business operations. This pressure sometimes results in careless or risky configurations like in the case of a merchant where, whenever there was a problem with the firewall, an IT employee would just apply the any/any rule while diagnosing the origin of the issue. Doing so left the merchant's network extremely vulnerable. And there is always the added risk of failing to disable/remove this rule once the testing process is complete.
Convenience and access vs. security
One experience left a security analyst stunned when after 4 years of audits with a longtime customer, they realized that after reviewing and approving the hundreds of firewall rules, the customer was changing the rules right after the security analyst left in order to give easier access to executives at the company.
Firewall security gaps are the rule
Our security analysts' experiences in the field reveal that firewall misconfigurations and security gaps are the rule, rather than the exception. Many breaches at large restaurants and retailers have originated from a firewall misconfiguration allowing outside traffic through.
If a company is determined to manage their own firewall or other security devices, it's crucial that those companies have a solid understanding of how to implement, manage and maintain these devices both conceptually and practically. It's even better if they consult with an experienced, properly certified provider for help managing their firewall. You would be surprised how often another set of trained eyes will notice a potentially serious vulnerability that would otherwise go completely undetected.
i-Comply Managed Firewall
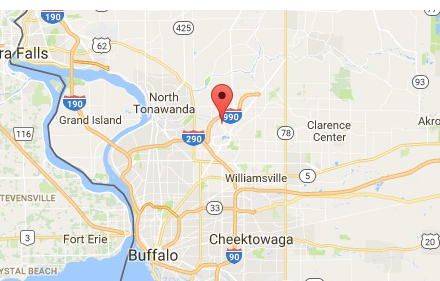
To protect your organizations' locations effectively, you need a closely managed firewall in place. With i-Comply, you’ll be alerted as potential threats are identified so you can stay secure at all your locations, protect your organization’s data, and meet compliance requirements.
i-Comply Managed Firewall includes:
· Managed security, not just visibility, for your extended network
· World-class firewall and internal vulnerability scanning technologies
· Managed firewall service to ensure that the firewalls are properly installed and working
· Proactive notification of outages and issue resolution
· Automatic network configuration backups for disaster recovery